The implementation methods for login and registration include the following in English:
1、Local Database: This method stores user credentials (like username and password) in a local database on the server. When a user registers or logs in, the system checks against the local database for validation.
2、Server-side Authentication: This involves validating user credentials on the server-side using various techniques like session management, cookies, and tokens.
3、Email Verification: After a user registers, an email is sent to their registered email address with a verification link or code. This ensures that the email address provided by the user is valid and helps prevent spam accounts.
4、Social Media Integration: Users can log in using their social media accounts like Facebook, Google, or Twitter. This method leverages OAuth or other APIs provided by social media platforms for authentication.
5、Multi-factor Authentication (MFA): This method requires more than one form of authentication to verify the user’s identity. It may include something you know (like a password), something you have (like a smartphone or hardware token), or something you are (like biometrics).
6、Single Sign-On (SSO): This allows users to use one set of credentials (like username and password) to access multiple applications or services without having to re-authenticate themselves each time.
7、RESTful APIs: Many authentication systems provide RESTful APIs that can be integrated into web applications or mobile apps for login and registration functionality.
8、OAuth 2.0: OAuth is an open standard for authorization that allows users to grant third-party applications access to their resources on another service without sharing their credentials. It is commonly used for social media logins and API integrations.
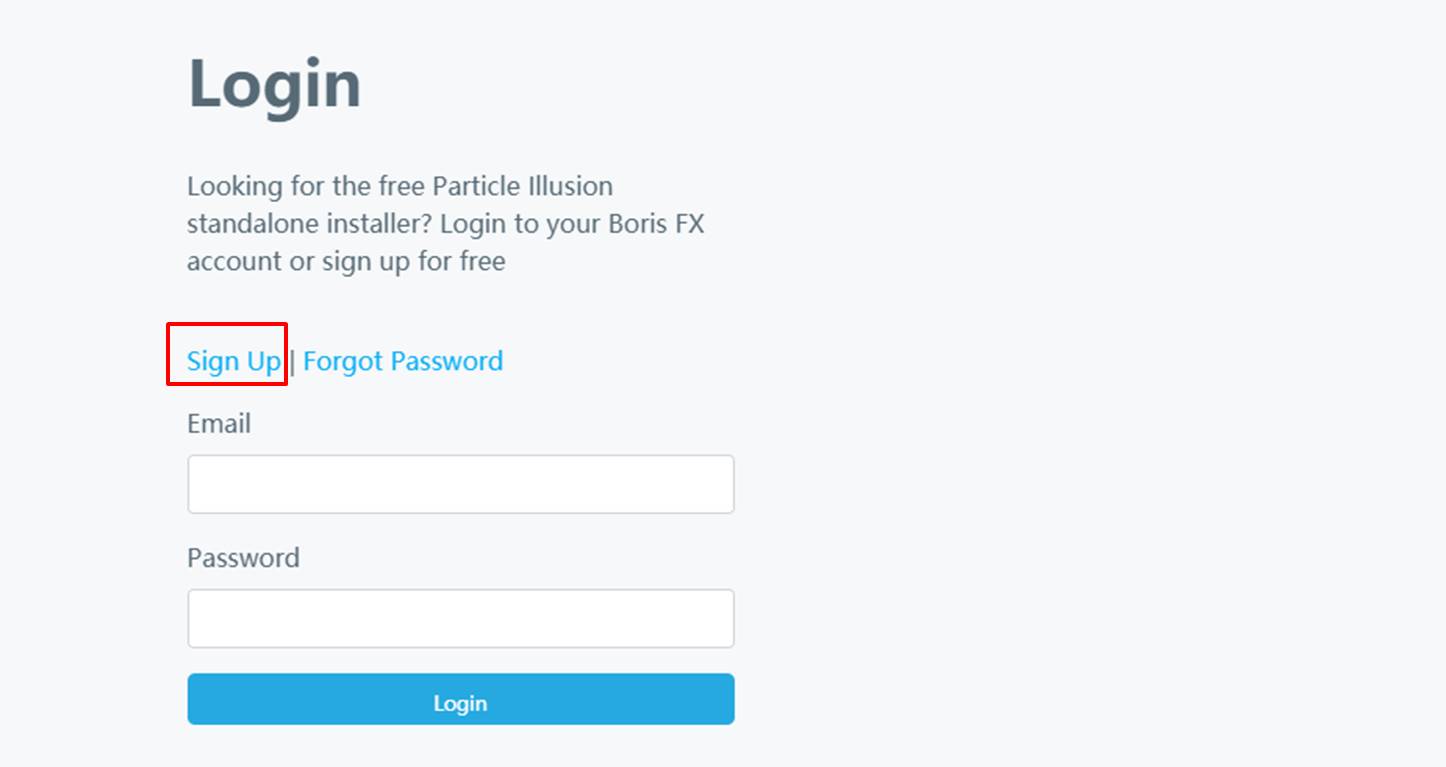
9、Password Reset Mechanisms: Implement methods like forgotten password or email verification to help users reset their passwords if they forget them.
10、Hashing and Salting: Store user passwords securely by hashing them with a salt (a random string added to the password before hashing) to prevent unauthorized access to sensitive data even if the database is compromised.
The choice of implementation depends on the specific requirements of the application, such as scalability, security needs, and user experience preferences.
 TIME
TIME
